Comments
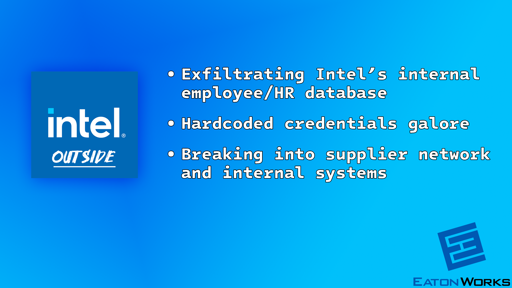
- It was possible to bypass the corporate login on an internal business card ordering website and exploit it to download the details of more than 270k Intel employees/workers.
- An internal “Product Hierarchy” website had easily decryptable hardcoded credentials that provided a second way to download the details of every Intel employee. More hardcoded credentials made it possible to gain admin access to the system.
- An internal “Product Onboarding” website had easily decryptable hardcoded credentials that provided a third way to download the details of every Intel employee. More hardcoded credentials made it possible to gain admin access to the system.
- It was possible to bypass the corporate login on Intel’s SEIMS Supplier Site and further exploit it to download the details of every Intel employee (the fourth way). Additional client-side modifications made it possible to gain full access to the system to view large amounts of confidential information about Intel’s suppliers.
You must log in or # to comment.
I almost feel bad for intel, they’re having a pretty bad year.
Almost. But the amount of anticompetitive behaviour they engaged in in their prime makes it hard to do.